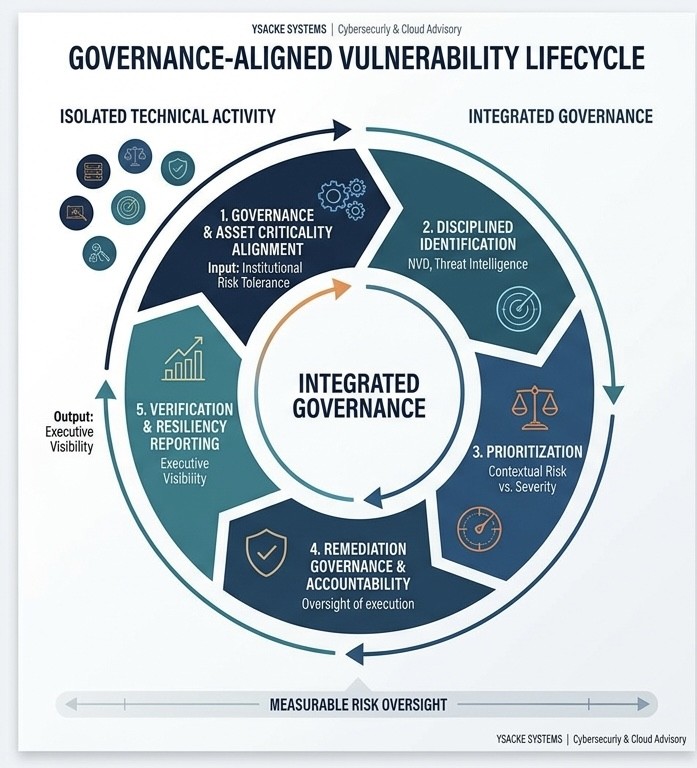
Cybersecurity programs fail when risk is measured inconsistently, ownership is unclear, and executive visibility is limited. YSACKE provides structured governance advisory that connects exposure data, remediation activity, and regulatory obligations into a unified oversight model.
Security teams often generate large volumes of findings without a defensible prioritization framework
We advise on the development of:
Security posture cannot rely on informal coordination. Effective governance requires clear ownership and defined oversight structures.
We support the establishment of:
Regulated and federal-aligned environments require defensible oversight models.
We align governance structures to:
Governance is not documentation.
It is measurable control over risk exposure, remediation execution, and institutional accountability.
YSACKE structures that control.
For regulated and federal-aligned environments, we structure cloud advisory in alignment with:
Cloud architecture must be defensible under audit — not simply functional
Cloud architecture does not operate in isolation. It must integrate with vulnerability governance, risk oversight, identity management, and executive reporting structures.
YSACKE ensures cloud security architecture is embedded within enterprise-wide governance frameworks — not treated as a parallel initiative.
This prevents fragmentation and preserves institutional accountability.
Secure infrastructure is not defined by provider selection — but by disciplined architectural governance.
YSACKE ensures cloud execution remains aligned with institutional governance, measurable risk tolerance, and defensible security posture.
Advisory capabilities are grounded in industry-recognized certifications and enterprise security